5 Fundamentals for Effective Security Design

In this article, we will cover the 5 basic fundamentals that are required for the effective security design in order to handle the organization in a reliable way as companies accelerate their digital transformation, network infrastructure edges – such as cloud services, LANs, SASEs, and many others are added to one’s security design. The connectivity continues to expand and fragment. Creating new vulnerabilities and possibilities for malicious hackers. So several businesses have amassed a plethora of confined security tools that are able to detect a particular function or safeguard a single segment of its network. CyberArk is the most effective security platform for securing the organization’s crucial data.
CyberArk is a software system with a powerful ability to meet companies’ cybersecurity necessities. Entities do not need infrastructure investment resources or strategic planning with CyberArk. Rather than, the CyberArk tool enables businesses to safeguard their access privileges and login information in a fast and efficient way. To be an expert in the network security platform or as a security analyst, CyberArk training would bring generous results.
Most new environments are crucial to addressing emergency business objectives, while others are frequently over-trusted and take off and land underneath the target list. Reducing the frequency at which change happens, there’s really very seldom sufficient time to incorporate it into an unified or thorough security plan.
Almost 80% of companies are incorporating a lot quicker than they can maintain them toward cyberattacks. Once safety is implemented in such a hasty manner. The process is a new network to restrict flexibility and control.
Traditional method lacks the effective security design:
Cybercriminals are looking for innovative ways to circumvent security measures and invade networks. One’s threats are becoming more sophisticated, angling to target multiple network corners at the same time in order to hide their potential attacks. And define the most easily manipulated connection in the target organization.
Number of diversified networks focusing on predominantly isolated point goods are unable to detect or protect against such attacks. The obvious problem would be that the disparate and separated vulnerability scanning. Implemented to maintain constantly growing and increasing system corners do not communicate with one another. This divergence generates scalability and reliability gaps, making it difficult to do and react to advanced and dispersed assault patterns with emphasis being placed.
5 Fundamentals for Effective Security Design:
The strategy to adopt security must change. Here seem to be five basic values and principles that now every company should follow in order to succeed of and take advantage of today’s security threats:
Fundamental 1: To develop and maintain authority across every edge, a security management fabric is mandated. It has to be capable of detecting risks, necessarily related data, as well as flawlessly impose policies. And practices all over a dispersed and constantly changing network. It’s not about selecting a fixed vendor; much more, it was about determining the best vendors. Emphasis should be given to suppliers who use application software (APIs) and common rules to support interoperability. Particularly those of us who enable strategy choices to be taken from outside their remedy.
Fundamental 2: Deployed security systems should also have access to shared datasets throughout all network edges, access points, and clouds. That are enhanced to true international and social environment security threats communicated all across company. This widely accepted intelligence approach allows holistic assessments of cost and reliability, recognizes potential threats. And allows for truly united reaction all across company.
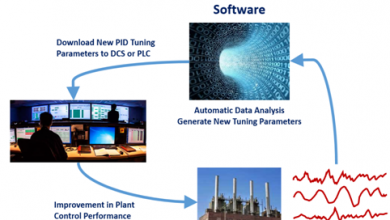
Fundamental 3: An interconnected security system must help facilitate sophisticated analysis of data. As well as the opportunity to develop new safeguards instantly across the entire assault cycle. Once those data analysis identify completely undiscovered potential risks. The whole process is intended to function independently in simplified ecosystems and also be related to alternatives for sophisticated network operations center but also dedicated security center (SOC) situations. Such as extensive detection, securing the data, event management, security orchestration, automation, and response building.
Fundamental 4: When an attack is perceived, the whole security fabric must be able to immediately release an organized threat response from across the ecological system. This interrupts the invasion series well before the goals can be met. Using artificial intelligence as well as machine learning in conjunction with drastically generated rulebooks enables it without trying to introduce downturns or human negligence.
Fundamental 5: So the only recurring theme in today ’s digital era is alteration. And a security fabric should be vibrant, which means it should be intended to ramp up as well as out with the system it’s really safeguarding transforms and adjusts. This necessitates seamless integration of computer and safety activities and processes in order for businesses to continuously innovate. As well as broaden interconnectivity and operational activities ecosystem services without the need for a delay in safeguards.
How security design strategies relies on the integration:
Security is perhaps most efficient in today’s highly complicated and ever-changing system whenever it provides broad knowledge and transparency. The very first step toward accomplishing this is to minimize downtime. Only then should developed data analysis, danger similarity, vibrant resilience, and interconnected risk response be enforced. These features, along with the capacity to be widely adopted, greater connection and integration among security features and safety as well as the network, and vibrant digitization amplified by AI, are indeed the cornerstones of every surveillance system able to defend today’s fast-paced systems and integrated ecosystems.
Conclusion:
In the above blog post we had covered the 5 basic fundamentals that are required for the effective security design in order to handle the organization in a reliable way. Go through, have any doubts drop your queries in the comments section.